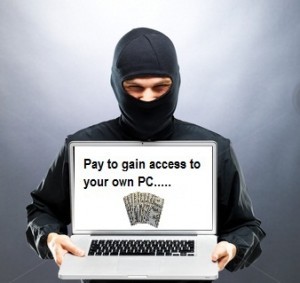
 The ransomware menace isn’t just escalating—it’s widening as well. We have seen a recent spike of reports on up-dates for current crypto-ransomware versions, in addition to findings of three fresh ransomware categories with new routines. This correlates with our forecasts regarding this growing risk, and how it can be a larger problem as cybercriminals up-date their tool-boxes in 2016 with fresh technologies.
The ransomware menace isn’t just escalating—it’s widening as well. We have seen a recent spike of reports on up-dates for current crypto-ransomware versions, in addition to findings of three fresh ransomware categories with new routines. This correlates with our forecasts regarding this growing risk, and how it can be a larger problem as cybercriminals up-date their tool-boxes in 2016 with fresh technologies.
Ransomware could be the biggest danger the security sector is confronting in today’s threat landscape. As a result, you must bank up more initiatives to prevent or combat it, or else you may be contemplating an arms race not just for security companies to defend against ransomware, but in addition for cybercriminals to set out more elusive and dangerous variants.
Newest ransomware updates include:
Offline Ransomware
Discovered to be directed at users in Europe and Russia since last year, this ransom ware has the potential to execute its routines off-line, without having to link to a C and C server. It manages by saving the RSA public key created in the encryption action in the meta-data of the encrypted data files. Afterwards, when the user chooses to pay, they have to send out at least one encrypted data file to the assailant’s email, to ensure the assailant can develop a decryption app based upon the public key saved inside the sent file.
Crytowall 4.0
Discovered in November 5 2015, the new up-date to Cryptowall provides the crypto-ransomware version enhanced communication abilities and modified code that enables it to manipulate more vulnerability. In addition it also revealed that the up-date also features an altered protocol that boosts its stealth capabilities
Power Worm
A new version of the ransom ware was found to have a defective encrypting process, on account of a mistake of the originator’s programming. The defect essentially throws away the encryption key which the criminal would keep hostage for the end user to settle ransom for. This implies the encrypted information is completely encrypted and difficult to recover. Paying out the ransom is inconceivable, so back-ups are the only option.
Chimera
An entirely new strain of ransom ware, Chimera contributes blackmail towards the extortion activity. Rather than just holding the end user’s files hostage, it threatens to post them on the internet if the ransom isn’t paid. However, research of the malware alone shows that the malware is not able of stealing anything or submitting any of the encrypted data into the cloud—this means that it is probably a scare tactic.
Linux Webserver Ransomware
Lastly, a completely fresh ransomware version was found to be targeting sites instead of computer hard drives. Inserted into web-sites through known vulnerabilities in website plug-in or third party applications, this virus then contaminates the host computer and encrypts the files in the home directories. In addition, it encrypts back-up directories and the majority of the system folders usually linked with the web-site itself. To avoid being caught in this high complex wave cyber threat its important that you take action to safeguard your company against new forms of Ransomware. Call I.T. Guys today at 405-748-0808 to protect your business from losing sensitive data
